Helcim API Tokens
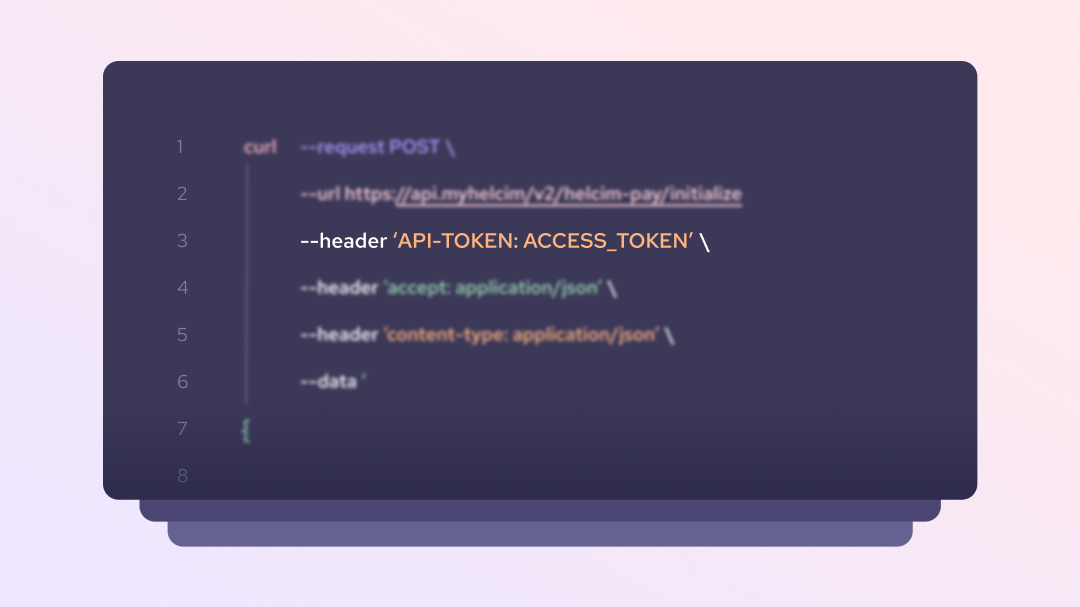
In order to use the Helcim API, a merchant or developer needs to login to the Helcim platform and create an API token for their production or developer test account. They must also set permissions on that access token to decide what functions that token can undertake when sending requests to the Helcim API.
API tokens should be protected by merchants and developers, as having access to a valid token gives a bad-actor the potential to process payments and make modifications to a merchant’s account. This is similar to why merchants should protect their password and not share it with anyone.
API token best practices
- We recommend obscuring your Helcim API token in your integrations backend environment files and never making this token visible in your client side code.
- When communicating with Helcim support and sending screenshots of code, or API requests and responses, we encourage merchants and developers to obscure all but the last 4 digits of their API tokens.
Helcim.js tokens:
To increase security when using Helcim.js, merchants integrating with this product should only allow verify transactions in their Helcim.js Access Configuration to tokenize card details and pass respective card tokens to the the Process Purchase Transaction API endpoint.
Compromised API tokens
If a merchant has their API access token compromised, they should either immediately disable it in the Helcim account settings, or generate a new token. These processes are outlined in our Modifying or Removing API Access Tokens documentation.
We would also recommend changing the passwords to access your Helcim account and ensure that only active and valid employees and developers have user access to the account.
Updated 4 months ago